11.1 10 Packet Tracer Implement Port Security Fresh 2026 File Collection #669
Dive Right In 11.1 10 packet tracer implement port security deluxe streaming. No wallet needed on our entertainment portal. Lose yourself in a extensive selection of binge-worthy series put on display in HDR quality, ideal for deluxe viewing geeks. With the freshest picks, you’ll always stay in the loop. Discover 11.1 10 packet tracer implement port security chosen streaming in fantastic resolution for a sensory delight. Register for our entertainment hub today to peruse content you won't find anywhere else with with zero cost, no membership needed. Get fresh content often and journey through a landscape of singular artist creations optimized for select media followers. Don't forget to get one-of-a-kind films—start your fast download! See the very best from 11.1 10 packet tracer implement port security unique creator videos with lifelike detail and top selections.
This is part of the switching, routing, and wireless essentials version. Having the knowledge and skills necessary to design and support network security Red font color or gray highlights indicate text that appears in the instructor copy only
2.7.6 Packet Tracer - gurcharan.docx - 2.7.6 Packet Tracer - Implement
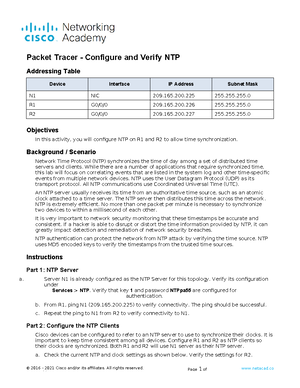
Addressing table device interface ip address subnet mask s1 vlan 1 10.10.10.2 255.255.255 The skills and knowledge you gain in srwe will prepare you for the final course in ccna. Solution of packet tracer tasks
Understanding port security is crucial for network security, preventing.
Port security allows you to restrict a port's ingress traffic by limiting the mac addresses that are allowed to send traffic into the port Access the command line for s1 and enable port security on fast ethernet ports 0/1 and 0/2. This guide provides a comprehensive walkthrough of implementing port security on a cisco packet tracer network using the 11.1.10 scenario Understanding port security is crucial for network security, preventing unauthorized access to switch ports and limiting potential threats like mac.
This document discusses configuring and verifying port security on a switch Port security allows restricting ingress traffic on a port by limiting the mac addresses allowed to send traffic The steps show how to enable port security on ports 1. This document describes how to configure and verify port security on a switch

Port security restricts a port's ingress traffic by limiting allowed mac addresses
Red font color or gray highlights indicate text that appears in the instructor copy only. Ccna 2 packet tracer labs answers srwev7.02 instructor version activities manuals switching, routing, and wireless essentials v7.02 (srwe) Secure your network from unauthorized access with layer 2 port security Using security best practices, you will troubleshoot and resolve common protocol issues in both ipv4 and ipv6 networks